SOC 2 Compliance in 2026: What Startups & SMEs Need to Know

SOC 2 has never been just a certification exercise. By 2026, that reality becomes harder to ignore. For startups and small- to mid-sized businesses, compliance is no longer treated as a future checkbox. It’s increasingly viewed as a signal of operational maturity. What’s changing isn’t the framework itself, but how it’s interpreted. Auditors, customers, and partners are paying closer attention to how controls function, […]
A Practical Guide on Prompt Injection – Part 1
What is Prompt Injection? Prompt Injection is a type of attack where an adversary manipulates the input (prompt) given to a large language model (LLM) in order to override its original instructions or security controls. In simple terms, the attacker tricks the AI into: This happens because LLMs prioritize user input commands over system-level instructions […]
Rate-Limit Bypass by Adding a Space: Simple Yet Abusable

Every application attempts to protect the Forgot Password feature from abuse. After all, nobody wants their inbox flooded with endless reset emails. Rate limiting is supposed to prevent exactly that. But sometimes, even solid security controls fail for the simplest reasons. This vulnerability is one of those “wait… seriously? 🤨” moments where adding just a […]
React2Shell: A Critical Vulnerability in Modern Frontend Frameworks
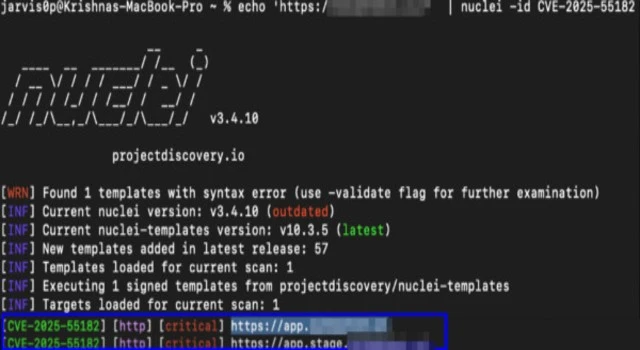
What is React2Shell (CVE-2025-55182)? A critical vulnerability with CVSS of 10.0 called React2Shell has been discovered in React’s Flight protocol that could allow attackers to execute arbitrary code on servers running React Server Components. CVE-2025-55182 affects multiple popular frameworks, including Next.js, React Router, React Server Components, and Waku, with exploitation possible under default configurations. Upon […]
AI-Driven Threat Modeling: Predicting Attacks Before They Happen

Cyberattacks are becoming more frequent and damaging in today’s digital space. Conventionally, security defenses completely depend on post incident responses that are not at all sufficient. Modern security teams are choosing AI threat modeling services as a proactive approach to predict, mitigate risks, and anticipate before they even materialize. By combining human insight with artificial […]
The Backdoor in the Cloud: Risks of Overly Permissive Azure SAS
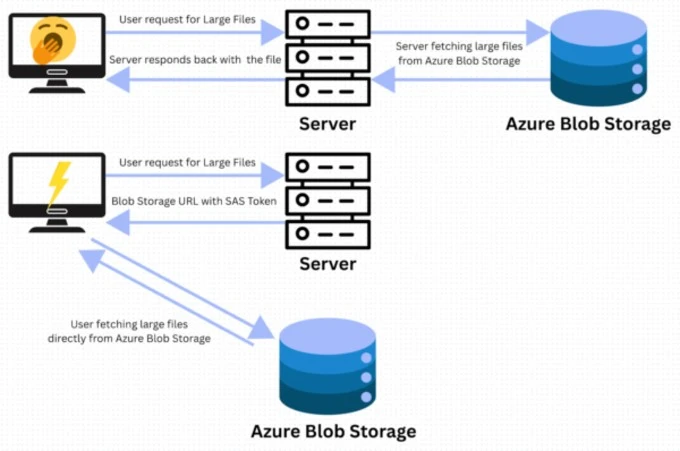
I. Executive Summary: The Quiet Catastrophe of Token Mismanagement Modern digital operations depend on massive data stores. Transactional data often sits in structured databases, while large volumes of unstructured content such as media, JavaScript assets, logs, and backups are kept in cloud object storage. Azure Blob Storage is a core service built for availability, scale […]
Beginners Recon Workflow for Bug Bounty & Web Pentesting
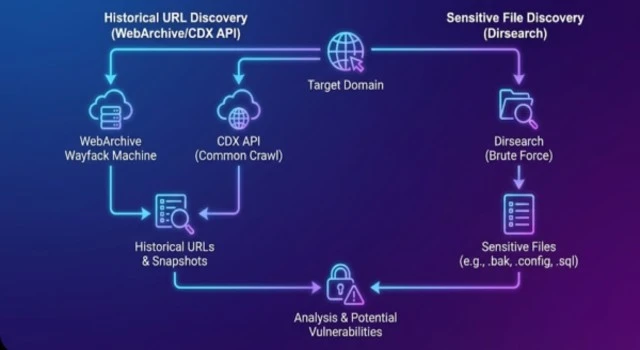
In bug bounty hunting and website penetration testing, having a strong and well-defined reconnaissance workflow is more important than just running random tools. Most security researchers fail to uncover high-impact vulnerabilities not because they lack skill, but because their recon process is unstructured. A proper recon workflow helps you systematically map the entire attack surface […]
SOC 2 Audit Failures: The Most Common Reasons Companies Fail — and How to Avoid Them

A SOC 2 audit is a crucial validation for all organisations dealing with customer data. It serves as an indicator that the organisation is applying safe and secure practices. On the other hand, a lot of firms do not pass the SOC 2 compliance audit due to a lack of readiness. The commonly made mistakes are neglecting […]
How to Automate SOC 2 Compliance: Tools, Workflows & Real-Time Gap Detection

SOC 2 compliance has become very important for companies that handle customer data. Many teams struggle because the process is time consuming and requires regular checks. A manual SOC 2 compliance audit often becomes stressful and slow. Such tools are recognized as the most widely used and effective solution nowadays, which is the reason for automation’s successful […]
DNS-Powered Stealth Malware: Unmasking “Detour Dog” and the Rise of TXT-Based Threats

Cybercriminals are no longer just breaking in; they’re learning to blend in. A new, worrying type of malware called “Detour Dog” hides by using parts of the internet that people usually trust. Instead of using obvious methods, it stores and receives information through DNS TXT records — tiny pieces of text that are normally harmless. […]

