From Zero to Audit-Ready: How Startups Can Prepare for SOC 2 & ISO 27001 Faster

Speed is the main priority for startups to proceed with product launches, getting new customers, and funding rounds. However, when security questions from enterprise clients or investors come up, a lot of founders find out that they are not prepared for an audit. Startups utilize and embrace reliable frameworks such as SOC 2 and ISO 27001 to establish their future growth and […]
The Dark Side of GraphQL: One Request Can Crash Your App

In 2026, if you’re testing a modern web / mobile application, there’s a very high chance you’ll encounter GraphQL APIs. From fintech dashboards and SaaS platforms to consumer-facing portals, GraphQL has become the default choice for API communication. Developers love it for its flexibility and efficiency. Frontend teams love it because they can fetch exactly […]
How to Automate SOC 2 Compliance: Tools, Workflows & Real-Time Gap Detection

SOC 2 compliance has become essential for companies that handle customer data. Many companies struggle because the process is time-consuming, requires regular checks, and often involves manually pulling information together at the last minute. A manual SOC 2 compliance audit can quickly become stressful and slow. That’s why automation has become the preferred approach; modern […]
SOC 2 Audit Failures: The Most Common Reasons Companies Fail — and How to Avoid Them

A SOC 2 audit is a crucial validation for any organisation handling customer data. It confirms that the business follows safe, consistent, and well-managed security practices. However, many companies still fail their SOC 2 compliance audit simply because they are not fully prepared. Common mistakes include neglecting key controls, failing to maintain proper documentation, and […]
TruffleNet in AWS: How Stolen Credentials Turn Into Cloud-Scale Fraud, and How to Stop It
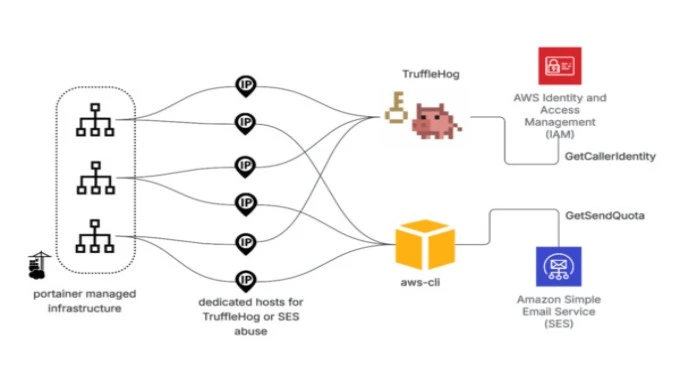
Introduction If you use AWS, remember that attackers frequently do not break in by hacking software. Instead, they usually log in with valid credentials. TruffleNet shows this clearly. Rather than using a single exploit, it works by using stolen AWS keys to test whether they work, then abusing cloud services, especially email, to make money […]
SOC 2 for AI Startups: Applying Trust Services Criteria to AI Products

The use of Artificial Intelligence, or AI, has been drastic and quick. The development of new products by AI startups is one of the major causes of this. Such products are capable of learning, thinking, and doing several other things for people. Acceptance of AI products by the public at large will not be possible without trust being built […]
How Long SOC 2 Really Takes: A Practical Timeline for 2026

SOC 2 timelines are often presented as predictable. Three months. Six months. Sometimes the timeline is shorter if the tooling is appropriate. In practice, that framing rarely holds up, especially for startups and small teams operating under constant change. By 2026, SOC 2 has settled into something closer to an operational maturity signal than a one-time compliance exercise. The framework itself hasn’t changed much. What […]
AI-Driven Threat Modeling: How Modern Teams Predict Attacks Before They Happen
Cyberattacks are becoming more frequent and damaging in today’s digital space. Conventionally, security defenses completely depend on post incident responses that are not at all sufficient. Modern security teams are choosing AI threat modeling services as a proactive approach to predict, mitigate risks, and anticipate before they even materialize. By combining human insight with artificial […]
The Human Hacker’s New Toolkit: Why AI Is Our Best Drone in 2025

Let’s cut the corporate jargon. In offensive security, 2025 isn’t about if AI changes vulnerability assessment and penetration testing [VAPT]; it’s about acknowledging that the threat landscape is now running at machine speed. If you’re still selling a static, three-week pen test, you’re selling a false sense of security that the adversary will exploit in […]
The Most Common SOC 2 Gaps Found in Startup Security Assessments

Most startups don’t fail SOC 2 because they ignore security. They fail because what they believe is “covered” isn’t operating the way they think it is. On paper, things look reasonable. Policies exist. Tools are in place. Access seems controlled. Then a security assessment starts. That’s usually when assumptions get exposed. A soc 2 gap assessment doesn’t uncover dramatic breaches. It reveals quiet mismatches between intention […]

