Mastering CSPT Detection: Automate Client-Side Security with Gecko and Advanced Analysis

cspt-detection-gecko-advanced-analysis
The Strategic Importance of SOC 2 Compliance in Today’s Digital Landscape

SOC 2 Compliance
Advanced Strategies for Effective Software Composition Analysis (SCA): Secure Your Open-Source Components

Software Composition Analysis: Securing Open-Source
Supply Chain Attacks and Third-Party Risk Management: A Critical Cybersecurity Imperative

Supply Chain Attacks and Third-Party Risk Management
Securing Multi-Cloud: Proven Strategies, Common Challenges, and Essential Tools.

Securing Multi-Cloud: Proven Strategies, Common Challenges, and Essential Tools
Governance, Risk and Compliance (GRC): Revenue Generation VS Loss Prevention

Governance, Risk, and Compliance (GRC)
Securing Open-Source Software: The Importance of Software Composition Analysis (SCA)

In today’s software development landscape, open-source components have become the backbone of modern applications. In fact, over 90% of apps rely on open-source libraries to speed up development. However, this widespread use introduces significant security, legal, and compliance risks if left unchecked. This is where Software Composition Analysis (SCA) steps in as a vital tool […]
Unlocking Success: A Comprehensive Guide to the Software Development Life Cycle (SDLC)
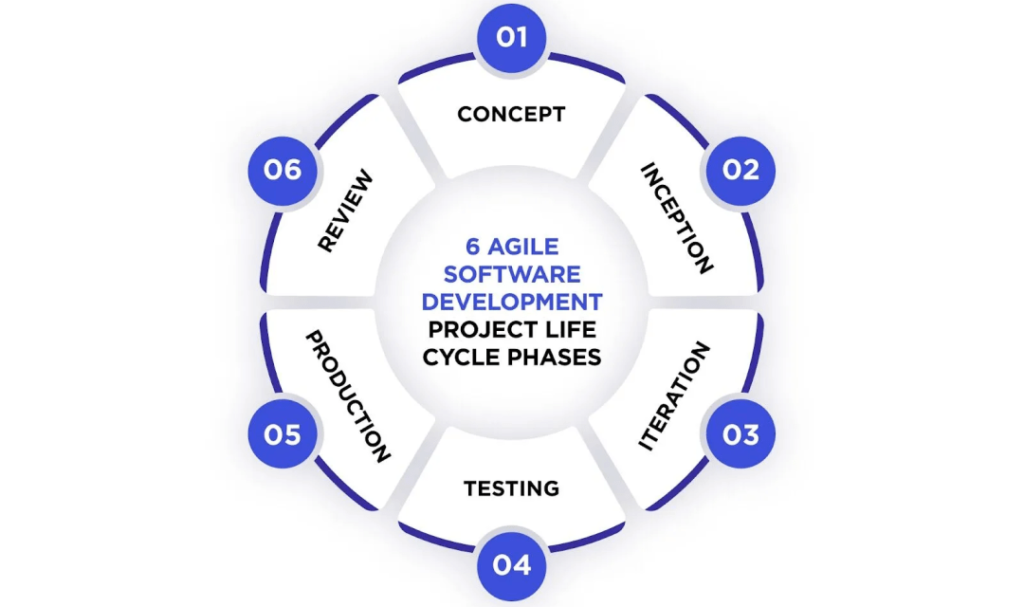
In today’s fast-paced tech world, the race to deliver high-quality software has never been more intense. Whether you’re a seasoned developer or just stepping into the realm of coding, understanding the Software Development Life Cycle (SDLC) is your golden ticket to creating successful applications. Think of the SDLC as your roadmap—it provides structure and guidance, […]
Understanding Cloud Security Posture Management (CSPM)

As businesses increasingly migrate their infrastructures to cloud platforms like AWS, Azure, and GCP, securing these environments becomes both critical and challenging. Cloud Security Posture Management (CSPM) is a powerful strategy designed to tackle these challenges by identifying, managing, and mitigating security risks across multi-cloud environments. What is Cloud Security Posture Management (CSPM)? CSPM combines […]
Decoding ISO 27001: A Comprehensive Guide to Information Security Management

Decoding ISO 27001: A Comprehensive Guide

